Conspiracy theorists like to imagine that computer viruses are written by anti-virus makers. That's because they don't actually understand the real reasons computer viruses are written--money, and lots of it. There's no need for antivirus vendors to risk their companies making viruses; the real virus writers are busy enough churning out malware to keep them employed forever.
I first published this article in my online journal on November 7, 2004. It details an infection of a Windows 2000 system belonging to my girlfriend with a particularly odius piece of malware called VX2, software which serves up ads on an infected computer and which goes to extraordinary lengths to prevent itself from being removed. The article traces the avenue of infection, the people responsible for the infection, and the people who profit from the distribution of malicious software like this.The original journal entry, which has generated quite a large number of responses, is here.
UPDATE 10-May-2006:
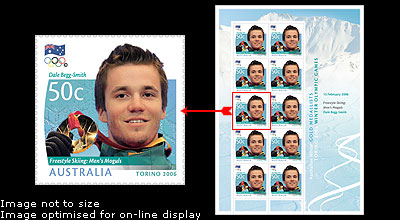
The nation of Australia has become the first country in the world to enshrine a spammer and computer virus writer on a stamp.
Australia has released a stamp featuring Dale Begg-Smith, the former Canadian who built an empire out of spam and infecting computers with malicious software, for his performance in the recent Olympics.
At about the same time, a new variant of VX2 has begun making the rounds. I've received a number of email reports about this new VX2 variant, which seems extremely resistant both to automated removal tools and to manual removal, and may be using "rootkit" techniques to conceal its files from Windows Explorer.
UPDATE 20-February-2006:
The amount of email I receive from this page has surged now that a man named Dale Begg-Smith, formerly a Canadian and a new Australian citizen, recently won a gold medal in skiing for the Australian Olympic team.
Why?
Because Begg-Smith, pictured here, is apparently owner of CPM Media, 2nd-thought.com, and the other organization that appear to be responsible for popup ads and the adware I document here. The connection between Begg-Smith and CPM Media is discussed on this page about Begg-Smith, and in this SpamKings article. In addition to the malware I talk about here, Begg-Smith and his company CPM Media have also been implicated in other malacious software installed by exploiting security holes in Internet Explorer via "drive by" downloads, including a keystroke logger Trojan called "FreeScratchAndWin" and a Web browser hijacker and adware program called "2nd-thought". This malware empire has enabled Begg-Smith to drive a Lamborghini and finance his Olympic medal bid, all by mucking up your computer.
UPDATE 18-November-2005:
I receive a lot of email about this page, and it's become a sort of "early warning system" for new versions of the VX2 malware. It seems that whenever a new version of VX2 is released, the amount of email I receive surges.
Based on the amount of email I've received from this page in the past couple of weeks, it appears a new variant of VX2 is on the rise. This new variant may employ rootkit-style cloaking or "stealth" techniques to hide itself; several people have reported to me that Ad-Aware indicates their system is infected with VX2, but can't locate the files, or that QAd-Aware locates the files but they cannot see the files Ad-Aware is reporting using Windows Explorer. If the program is using rootkit-style cloaking to conceal itself, I can't think of any easy ways to remove it save for installing the hard drive from the infected computer into another computer and searching for the files that way.
Several people have emailed me to say that in addition to spreading through browser exploits and other security exploits, VX2 is more and more often being spread along with other files on peer to peer file sharing networks. People downloading files from P2P networks may be infecting themselves with VX2 as well.
I've also updated some of the information on this page. Updates to the page on November 18 will be indicated with [Update].UPDATE 20-June-2005:
I've posted additional information about techniques to remove VX2 from an infected computer in the removal section here. There also appears to be a relatively new VX2 variant in circulation which is even more difficult to remove than the variants I've encountered so far.I've also received a demand letter from an attorney claiming to represent the persons named in the email I've received from the person mentioned below. This demand letter is claiming defamation. On the advice of my attorney, I've removed that email until such time as this all gets sorted out.
UPDATE 23-May-2005:
This page has resulted in a very high volume of emails, most of them expressing frustration and anger on the part of computer users infected with VX2. Recently, I've received an email from a person who says he once worked for the author of VX2. The contents of that email, which I have been given permission to post, are here (note: this email is no longer available pending further consultation with my attorney).Information about removing VX2 from an infected computer is here.
There is lots and lots and lots of money in computer viruses and spyware, especially the variety that makes popup ads appear on your machine. The question I've always had, though, is who's making all this money by infecting your computer?
A couple nights ago, Shelly's computer became infected. Shelly's technically savvy, the apartment we live in is on a closed private network with a hardware firewall between us and the Internet, and she also runs a software firewall on her computer, and she still became infected nonetheless. I spent about six hours removing the infection, and also tracking down the source of the infection, and painstakingly backtracking all the popup ads that the adware displayed on her computer.
My goal: Follow the money. Discover where the infection came from, and who was making money from it. The results were, to say the least, interesting. If you don't care about stuff like this, you can skip the rest of this message. If you're curious about the mechanisms by which spyware and viruses work, who is responsible for them, why they're so common, how they spread, and most important, who makes money by creating and releasing them, read on!
Shelly's computer started behaving strangely, taking a long time to boot and displaying popup ads whenever she launched Internet Explorer, late Wednesday afternoon. Running the anti-spyware program Ad-Aware revealed that the computer was infected with a very nasty bit of malware called VX2, first introduced to the Internet public by a company calling itself VX2, which has since become defunct.
The VX2 program has continued to be developed and to become nastier, more destructive, and more malicious as time goes on; today's VX2 is extremely sophisticated, highly destructive, and almost impossible to remove. Ad-Aware and a similar program called Spybot Search & Destroy could see the infection, but could not remove it. VX2 remains memory-resident, even if its files are deleted, and constantly monitors attempts to get rid of it; if it is removed or the computer's Registry is changed, this evil little bastard changes the Registry back and rewrites itself to disk under a different name. It also sets itself up as a critical system service (so it runs even when the computer is booted in safe mode), and cloaks itself so that it does not appear in the Task Manager.
Earlier versions of VX2 could only conceal themselves in the Task Manager under Windows 95/98/Me; VX2 Variant 3 appears to be able to conceal itself in the Task Manager under Windows NT/2000/XP as well.
Ad-Aware has a special plug-in module written especially to remove VX2. This plug-in confirmed that Shelly's computer was infected with what it described as "VX2 Variant 3," but even the plug-in could not remove the infection; it appears that Shelly had become infected with a brand-new VX2 variant, more cunning and more malicious than even the worst variant known to Ad-Aware. But from where?
Now things get interesting. In following the source of the infection, I ended up in a virtual trip that went from Dallas, Texas, through servers in Russia and Nevada, and finally back to the source in Rosemount, Minnesota. Along the way, it involved a surprising number of big-name, supposedly reputable companies, all of whom are profiting either directly or indirectly from viruses and spyware.
Shelly's computer first became infected when her browser visited the Web address "http://69.20.56.3/ normal/yyy12.html". At the time I am writing this, this Web address is still active.
[Update]: It appears that this URL is no longer active. Nevertheless, I have opted to continue putting a space in the URL (the original URL contained no space) to prevent people from inadvertently visiting it in the event it becomes active again in the future.
I don't know what brought her to that site; it may have been a redirect, a browser hijack, even a maliciously constructed banner ad.
The site infects a computer using an Explorer iFrame exploit. Put most simply, if a Web page contains an iFrame that points to another Web page containing an OBJECT tag, the file referenced in the OBJECT tag (in this case, a dropper for VX2) is downloaded and installed silently, without the user's knowledge or consent. Versions of Internet Explorer prior to the version that shipped with Windows XP SP2 are all vulnerable; I have not tested the version of Explorer that shipped with XP SP2 or versions patched by subsequent security fixes. I do know that Microsoft has since closed several iFrame exploits. I do not know if this exploit is one of them.
[Update]: I have now verified that this security hole has been fixed in the version of Internet Explorer 6 that is current as of the time of this writing.
The Web site at 69.20.56.3 is running on a computer whose ISP connection is provided by a company called Rackspace, a large and busy Texas-based ISP with international offices and a long history of supporting and condoning spam and other unethical behavior; in fact, Rackspace even had its own entire section on the old Blackholes.us spam support blacklisting service.
So Rackspace is the first company profiting from the infection; they're making money by providing Internet connections for the URL hosting the malware dropper. Remember the name Rackspace; we'll be seeing it again later.
So. Moving along: The virus-dropping Web site at 69.20.56.3 is nothing but a simple redirector. It redirects to "http://213.159.98.203/ ads/banners/banner3.php?ID=1". Again, I have put a space in this URL.
[Update]: It appears that this URL is also no longer active. Again, I have opted to continue putting a space in the URL (the original URL contained no space) to prevent people from inadvertently visiting it in the event it becomes active again in the future.
This page is referenced by an iFrame from the preceding page, and contains an iFrame pointing to the next server in the chain, which contains the actual dropper; we'll get to that in a moment.
This Web site is hosted on a server in Russia; the ISP is a Russian service called Linkey.ru. They are the second group of people in the chain making money from viruses and spyware, by hosting a virus dropper. I don't know if they're a knowing participant or just an innocent ISP who's unknowingly hosting a virus dropper.
Additional information from a helpful reader on the news.admin.net-abuse.email newsgroup: The Russian-hosted Web site is:
http://213.159.98.203/ = Adsavior.com 11/08/04 11:05:06
dns Adsavior.com
Adsavior.com NS (Nameserver) ns1.adsavior.biz
Adsavior.com NS (Nameserver) ns2.adsavior.biz
Adsavior.com A (Address) 213.159.98.203
mail.Adsavior.com A (Address) 213.159.98.209
ns1.adsavior.biz A (Address) 213.159.98.204
ns2.adsavior.biz A (Address) 213.159.98.208Organization: Adsavior Inc.
James Finlayson
#395-1027 Davie St.
Vancouver, BC V6E4L2 CA
Phone: 6046969057
Email: jamesinflames69@hotmail.com
Registrar Name....: Register.com
Registrar Whois...: whois.register.com
Registrar Homepage: http://www.register.com
Domain Name: ADSAVIOR.COM
Created on..............: Thu, Sep 16, 2004
Expires on..............: Fri, Sep 16, 2005
Record last updated on..: Mon, Oct 04, 2004It appears that linkey.ru and IPs in the same general block as "Adsavior.com" are well known for Net abuse. Mr. Finlayson, another Canadian, appears to be deeply involved in this particular virus/adware gang as well.
[Update]: Somewhere in the time between the last time I checked these URLs and now, Rackspace and Linkey.ru have taken down these sites. 69.20.56.3 and 213.159.98.203 no longer have active Web servers running on them. It took months, however, before these sites were taken down, and it's not clear whether they were removed by the ISPs, or simply removed because they were no longer useful to the malware distributors.
Onward and upward: The Russian virus host itself is also nothing but a redirector. Clearly, the person responsible for the virus wants to put some distance between himself and the virus; we've already gone through two redirectors in two countries.
The Russian Web site contains an Internet Explorer iFrame exploit which causes Internet Explorer to load a program from the URL "http://www.xzoomy.com/ stc.php?stid=007". Once again, I have put a space in the URL; if you visit this Web site, and allow your browser to download the executable that it references, you'll be infected with VX2.
[Update]: This Web site is still live and functioning. This URL will still infect your computer as of the time of this writing.
Now we're getting somewhere. The xzoomy.com Web site is a search engine that's well-known in anti-virus and anti-spyware circles. Xzoomy.com makes a small profit every time someone uses their Web page to do a search; they have a long and ignoble history of attracting visitor through the use of spyware, adware, and viruses. They've been responsible for their own spyware/adware software, and they've got their hands in an Internet gambling site called "free scratch and win" as well. These guys are looking more and more like our scumbags, eh? This site is registered to:
So Mike Cass is up to his ears in this mess. Mike's Web site, well-known for being the source of spyware and adware, is hosted by an ISP called Peer 1 Network, an outfit in Montreal known to be indifferent to spammers. Mike and Peer 1 Network are making money here--Peer 1 by hosting Mike's Web site in spite of the fact that it's known to be associated with adware and spyware, Mike because he makes money every time someone visits his site.XzoomY.COM
Mike Cass (domains@adscpm.com)
+1.2042984015
Fax: +1.0000000000
181 Coniston St
Winnipeg, MB R2H1P8 CA[Update]: It appears that XzoomY.com is actually simply an alias to the same IP address also hosting 2nd-thought.com discussed below and CPM Media's Web site, also discussed below.
But wait, there's more! The xzoomyy.com Web site is another redirector. It redirects to "http://www.2nd-thought.com/ files/install007.exe" (I've put a space in the URL); and it loads and executes the Windows program install007.exe from the 2nd-thought.com Web site by using an OBJECT tag.
This file, install007.exe, is the actual executable that installs the adware. If you're using Explorer for Windows and you visit any of the pages before this in the chain, install007.exe downloads and runs silently without prompting you, because the OBJECT tag that references it is contained inside an iFrame. This is also why other browsers are safer; they don't recognize the iFrame tag.
The program install007.exe loads and runs as soon as the browser hits that page; the computer's owner never gets any warning and has no opportunity to stop it. As you may have guessed, install007.exe installs VX2 on the victim's computer. Note that all this--the numerous redirects, downloading the program from the 2nd-thought Web site, installing the VX2 virus--all happened automatically and silently; at no point is the computer owner aware of what is going on, and at no point does the computer owner know that a virus is being loaded onto his computer.
2nd-thought.com is the primary villain here. They are hosting the installer itself; they are the people actually placing VX2 on the victims' computers without permission or notification. Let's take a look-see and find out who these guys are:
Well, lookit that, another Canuck. What is up with Canadian spyware and virus profiteers, eh? Does Canada have particularly lax computer-crime laws?Domain name: 2nd-thought.com
Registration Service Provided By: CPM Media, Ltd.
Contact: domains@adscpm.com
Registrant Contact: Don Lativalle (abuse@2nd-thought.com)
+1.5198514015
Fax: +1.0000000000
3597 boul St-Jean
Dollard des Ormeaux, H9X2B5 CA
[Update]: A Google search for "Don Lativalle" reveals that he is well-known to security firms and adware firms. This page in the eTrust Spyware Encyclopedia names him as the person responsible for another Trojan horse program, and says that he is affiliated with a company called CPM Media--which is consistent with the domain whois information above. This page at the WebHelper Watcher List links Don Lativalle, CPM Media, and xzoomy.com.
CPM Media is reported by many people to use security exploits and vulnerabilities to install adware and spyware on people's computers. For example, webhelper4u.com details this malware which installs itself using a security vulnerability in Windows Media Player and redirects visitors to a CPM Media Web site.
It may be that "Mike Cass" and "Don latville" are pseudonyms for Dale Begg-Smith, or it may be that they are people working for Begg-Smith. In either case, it seems clear that these names are associated with CPM Media, Begg-Smith's company.
2nd-thought.com is hosted by Peer 1 Networks as well. 2nd-thought.com is also a well-known scourge on the Internet, notorious for releasing a spyware program that changes your home page to their page, and for redirecting search engine searches you do to porn sites.
That's two scumbags with long histories of Internet abuse, both hosted on Peer 1 Networks and both, apparently, now working together. Mike Cass, Don Lativalle, and Peer 1 Networks: three people or organizations with shady pasts and questionable ethics, three people or organizations who are apparently involved with loading VX2 onto Shelly's computer.
So now we know how VX2 ended up on Shelly's computer. We know what people are responsible, we know what businesses support and profit from them, and we know they've gone to a whole lot of trouble and effort to hide themselves.
We know that the people, Mike Cass and Don Lativalle, have histories of releasing spyware and adware to infect people's computers, we know they run for-profit Web sites, and we know that they have independently established histories of using dubious and unethical practices to get traffic to those Web sites. We know they're both Canadian, we know they have found a Canadian ISP in Peer 1 Networks willing to turn a blind eye to outrageous network abuse, and we know that they appear to have teamed up to spread an extremely malicious variant of a program already known for being almost impossible to get rid of.
What's left is discovering the why. What's the mechanism by which they make money? How do they profit from infecting you with VX2? Where does the money come from, and where does it go? For that, I had to turn to the actions that this VX2 variant takes once it's infected the computer, and to the ads it serves up.
This particular strain of VX2 does two things. First, it carries a payload unusual for adware; it loads another adware program called Bargain Buddy. Bargain Buddy's Web site was at cashbackbuddy.com, which was hosted by Globix, a Web-hosting company that was headquartered in the United Kingdom. (Since writing this, it has gone bankrupt, proving one more time that the normal course of business of spam and malware hosting firms is to go out of business. Cashbackbuddy.com lived on for a time at GoDaddy, but now redirects to a page that says "eXact Advertising is no longer distributing any software and has not distributed any software since mid-2006.") The cashbackbuddy.com Web site attempts to get people to deliberately infect themselves with the Bargain Buddy scumware by telling them "the new Software helps the end-user maximize his/her savings and gain cash back commissions from purchases made at all participating on-line and some offline merchants" (and so on, and so on). CashBackBuddy and its scumware is operated by an outfit called eXact Advertising:
eXact Advertising owns a number of different Internet properties, including pay-for-placement search engines, Mail.com, a personals Web site called "luvbandit," and so on.eXact Advertising
101 W. 23rd Street, PMB 2392
New York, New York 10011
United States
646-223-1227
[Update]: eXact Advertising is now the target of a class action lawsuit alleging that they used illegal tactics to install their software on people's computers via security exploits.
The Bargain Buddy software is pretty straightforward: every now and then, it loads an ad on the victim's computer. Each time an ad is served, eXact Advertising makes a few cents from the advertisers who pay for the ads. Some of this money goes to Bargain Buddy "referrers;" the rest is profit. So what that means is that if I sign up with eXact Advertising, then I get you to put the Bargain Buddy adware on your computer, every time an ad pops up, the advertiser pays eXact Advertising some money, and eXact Advertising pays me some money.
eXact Advertising claims to be "opt-in;" they say the only way you'll get Bargain Buddy is if you explicitly sign up and put it on your computer voluntarily. They lie, of course; the fact that they're doing businesses with referrers such as Mike Cass and Don Lativalle, who use very sneaky ways indeed to get the software onto your computer, proves it. They pretend to be good guys helping consumers save money; in reality, they don't care so long as people can be cajoled, tricked, or forced into installing their software, with or without their consent.
So. Now Shelly's computer is infected with two adware programs: Bargain Buddy by eXact Advertising, who is paying the people responsible for the infection, and a custom version of VX2, which prevents itself from being removed easily, installs Bargain Buddy, and also serves ads on its own.
Now popup ads are popping up all over the place. Some of them are from eXact Advertising, a shady company that's written its own custom adware. Some of them are from VX2 itself. It's the latter ones, the ones that VX2 is generating, that are the most interesting.
VX2 brings in ads from, of all places, Revenue.net, a very large mainstream online advertising broker that serves up banner ads, popup and popunder ads, and contextual ads for a lot of big-name clients. Revenue.net does serve popup ads and popunder ads, primarily from Web sites rather than adware.
The ads being brought in from the VX2 infection were being pulled from Revenue.net; the persons responsible for the VX2 infection were Revenue.net affiliates. I fired off an email to Revenue.net, with the URLs of some of the popup ads being pulled in by the virus. Revenue.net, rather to my surprise, actually responded, and claimed that the affiliate code attached to the popup ads appearing on Shelly's computer belonged to an outfit calling itself "look2me.com".
Look2me.com is--surprise surprise--a Web advertising company that makes money from popup ads. Look2me.com is a Revenue.net affiliate; Look2me.com gets people to view ads produced by Revenue.net, the advertiser pays Revenue.net, who then pays a percentage of the take to look2me.com. Look2me.com is hosted by...
wait for it...
Rackspace! Told you their name would pop up again.
Look2me.com is owned by:
NicTech Networks also owns a dating service called "SimilarSingles.com". Sound familiar?NicTech Networks
info@look2me.com
3860 W 150TH ST
Rosemount, Minnesota 55068
United States
866-705-2728
eXact Advertising, based in New York, is an Internet advertising company that serves popup ads on virus-infected computers and also owns an online dating service. NicTech Networks, based in Minnesota, is an Internet advertising company that serves popup ads on virus-infected computers and also owns an online dating service. Two well-known and unethical Canadians, Mike Cass and Don Lativalle, each with separate histories of profiting from adware and malware, are jointly responsible for a computer infection which serves popup ads from eXact Advertising and NicTech Networks. NicTech Networks is hosted by Rackspace; the initial point of infection of the virus is a Web site hosted by Rackspace.
Rackspace is looking pretty bad here. In fact, Rackspace and Peer 1 Networks are both obviously dirty; both are up to their elbows in hosting and providing services for people who make money by serving popup ads through viruses and malware.
It's hard to argue that either Rackspace or Peer 1 Networks is simply being duped by a client, particularly in light of the fact that emails to both outfits concerning this situation go unanswered, and in light of the fact that the virus-dropping Web site is still up three days after I've emailed the responsible hosts.
After complaining to both ISPs, I still have not had a response from either. As of this writing, neither Rackspace nor Peer1 has taken any action against the Web sites named in this report.
So. Advertisers pay eXact Advertising and Revenue.net. eXact Advertising and Revenue.net then go on to pay affiliates who have infected target computers with malware to serve up the ads. The affiliates host their virus-dropping Web sites, along with Web sites that profit in other ways from viruses and malware, on Canadian ISP Peer 1 Networks and American ISP Rackspace.com. The money goes from the advertisers to eXact Advertising and Revenue.net; some of this money then goes to the affiliates, who infect the computers with malware; some of the money the virus-spreaders make in turn goes to Peer 1 Networks and Rackspace, who turn a blind eye to what their clients are doing.
But where does the money originate? Obviously, the advertisers are only buying ads because they think the ads will work; that means, somebody is clicking on these popup ads and buying the advertisers products. But who on earth would spend money on an annoying popup ad? What could possibly induce someone to take out his wallet when everyone knows that virus-spawned popup ads are among the most annoying things on Earth?
Ah, that's the pure genius of it--that's the brilliance of the scheme, honed to a fine edge. The popup ads you get when you're infected with VX2? They advertise...
...spyware removal and popup blocking tools.
ADDITIONAL BACKGROUND INFORMATION ABOUT VX2
I recently received an email from an individual, who's asked not to be identified, who says he used to work with the people responsible for the creation of VX2. I've received permission to reproduce the contents of that email, minus personally identifying information; the contents of the email are below.
[removed on advice of my attorney]
...can be a nightmare. There are several variants of VX2; each is more sophisticated than the last at preventing itself from being removed. Almost all VX2 variants hide themselves by patching the Task Manager, so their processes do not show up when you bring up the Task Manager; some of the later versions also conceal themselves from Windows Explorer, so you can not see the viral files on your hard drive even if you know where they are and what they're named.
One thing all VX2 variants have in common is that they are virtually impossible to stop on an infected machine. VX2 loads even when a Windows computer is booted in "safe mode." It's characterized by having multiple processes which watchdog each other and the system Registry; if one VX2 process is terminated, it's re-started by the other, and if the Registry is modified to remove calls to VX2 while VX2 is running, it immediately rewrites the Registry to add itself back.
VX2 is also polymorphic, in the sense that its executable files may be renamed each time the computer is restarted or shut down.
The earliest VX2 variant can be removed by LavaSoft's Ad-Aware, which is available at download.com. VX2 variants 2 and 3 can not be removed by Ad-Aware alone, but can often be removed by the Ad-Aware VX2 Plugin. (Be sure to follow the instructions precisely when using this plugin!) Later variants can not be removed even by this plugin. I've not had any success removing any variant of VX2 using Spybot Search & Destroy. I'm told that Microsoft's anti-spyware application can remove some variants of VX2, though I have not tried it myself.
[Update] At least one variant of VX2 appears to be quite resistant to the removal method which is described below. It appears this variant may write itself to the hard drive, usually to the directory \windows\system, multiple times, but invoke only one copy of itself at any given time; if the copy which is currently running is removed, a different copy is invoked on system startup. Therefore, it may be necessary to use the technique described below to delete not only the current copy of VX2 but any additional copies as well. You may be able to identify these VX2-related files by looking for files in the \windows\system directory which are identical in byte length to the copy you've identified using Ad-Aware. Rename these to something else, so that you can restore them if they are in fact part of the system rather than part of VX2.
Removing VX2 in cases where applications such as Ad-Aware have failed requires either access to another computer, or access to a bootable floppy disk. You can create a bootable floppy using Windows; the process is different for different versions of Windows, and is explained in Windows Help.
If you have access to either a bootable floppy or to a second computer, the process goes like this:
- Run Ad-Aware on the infected computer. After it completes the scan, Ad-Aware will report a VX2 infection; most likely, there will be many such reports, detailing all the system Registry entries for VX2. One of the lines in the report will also identify the file, which is usually in the Windows\System directory, and may look something like this:
C:\Windows\System\gxvcdb.exeNote that the filename will be different; it is created at random. Write down the path and filename.
- Do not allow Ad-Aware to attempt removal; doing so will cause VX2 to change its name. As soon as you have identified the file, pull the plug on the computer. Don't try to use the Shut Down command; this may cause VX2 to change its name.
- Remove the hard drive and insert it as a slave drive in another computer that is known to be clean, or boot the computer using the boot floppy. It is absolutely vital that you have some way to start the computer cleanly and without VX2 (either by using a second computer known to be clean or by using a boot floppy that's known to be clean), because otherwise it may not be possible to remove the file. (Note: If your computer is a laptop, it may be difficult or impossible to install its hard drive in another computer, and you may not have a floppy drive. In that case, you may need to use a bootable CD, such as a full installer CD for Windows XP or a Linux boot CD, and use the Windows Recovery Console or the Linux terminal to remove the offending file(s). The Windows Recovery Console offers a command-line prompt which will allow you to navigate to the directory on the C drive where VX2 resides, and rename or delte the VX2 file.)
- Navigate to the directory identified by Ad-Aware and delete the offending file; in the example above, this means removing the file "gxvcdb.exe" from the System directory inside the Windows directory.
- Replace the hard drive in the original computer or remove the boot floppy and reboot the computer. Run Ad-Aware again to verify that the infection has been removed.
I've also received an email from at least one person who's had success against some VX2 variants by using the following method, which may be worth a first shot at dealing with a VX2 infection:
- Identify the VX2 file itself, using Ad-Aware or a similar tool, as described above.
- Using Notepad, create an empty text file with the same name (for example,
gxvcdb.exe) and save it to your Desktop. - Open the folder that the VX2 file exists in (for example,
c:\windows\system) - Kill the process and delete the file, by telling Ad-Aware to remove the infection or (if possible) by using the Task Manager (note: some VX2 variants "stealth" themselves and will not appear in the Task Manager).
- Immediately drag the file with the same name from the Desktop to the Windows\System folder. You must do this quickly, before the "watchdog" process has an opportunity to rewrite the file.
- Reboot. If you see warnings about an invalid program when the computer reboots, you've successfully replaced the VX2 file with the bogus text file of the same name. At this point, VX2 is not running; you can edit your Registry to remove the reference to the VX2 file (it will likely be in HKey_Local_Machine\Software\Microsoft\Windows\run) and delete the text file.
[Update]: It appears that new VX2 variants are using .dll files rather than .exe files; that Ad-Aware may not be able to identify the files it is using; and that in some cases Ad-Aware can identify the files, but if you look in the directories wherer Ad-Aware claims the files are located, you can't see them. I have not personally encountered this variant of VX2 yet, but if this is true, it suggests that VX2 is now using a rootkit or some similar technique to conceal itself. I'm told that Ad-Aware and Spybot S&D can not at present remove this variant of VX2, and that the texhniques listed here may not remove it either. If it is using rootkit-style techniques to conceal itself, you will probably need to remove the hard drove of the infected computer and connect it as a slave drive to an uninfected computer in order to be able to see and delete the VX2 files.
Anyone with additional information on VX2 may reach me by email. If you have comments or questions, please feel free to email me or to reply in the LiveJournal entry regarding VX2.